French company Quarkslab specialist Adrien Guinet reports that he has found a way to decrypt data damaged by a ransomware attack. Unfortunately, this method only works for the Windows XP operating system and not in all cases, but it is better than nothing.
I got to finish the full decryption process, but I confirm that, in this case, the private key can be recovered on an XP system #wannacry!! pic.twitter.com/QiB3Q1NYpS
Guinier published the source code for a tool he called WannaKey on GitHub. The researcher’s technique is, in fact, based on the exploitation of a rather strange and little-known bug in Windows XP, which even the authors of the sensational ransomware malware did not seem to know about. The fact is that, under certain circumstances, it is possible to extract the key needed to “rescue” files from the memory of a machine running XP.
The researcher explains that during operation, the ransomware uses the Windows Crypto API and generates a pair of keys - a public one, which is used to encrypt files, and a private one, which can be used to decrypt files after paying the ransom. To prevent victims from getting to the private key and decrypting the data ahead of time, the authors of WannaCry encrypt the key itself, so that it becomes available only after payment.
After the key has been encrypted, its unencrypted version is erased using the standard CryptReleaseContext function, which in theory should also remove it from the memory of the infected machine. However, Guinier noted that this does not happen, only the "marker" pointing to the key is removed.
The specialist writes that it is possible to extract the private key from memory. Guinier himself conducted a series of tests and successfully decrypted files on several infected computers running Windows XP. However, the researcher writes that for a successful outcome of the operation, a number of conditions must be met. Since the key is stored only in volatile memory, you need to be wary not only of the fact that any process could accidentally overwrite data on top of the key and the memory will be redistributed, but you also should not turn off and restart the computer after infection.
“If you are lucky, you will be able to access these areas of memory and recover the key. It may still be there and you can use it to decrypt your files. But this does not work in all cases,” writes the researcher.
It is unknown how many computers running Windows XP were infected with WannaCry, and what percentage of users never rebooted or turned off their PC after infection. Let me remind you that in total hundreds of thousands of machines were affected by ransomware attacks in more than a hundred countries around the world. Still, Guinier hopes his technique could be useful to at least some users.
Other experts have already confirmed that in theory the Guinier instrument should work. Thus, the famous cryptographer and professor at Johns Hopkins University Matthew Green writes that the method should work, although in the current circumstances it all looks more like a lottery. Another well-known specialist, an employee of the F-Secure company, Mikko Hypponen, asks the question “why use a function that does not destroy keys to destroy keys?”, but agrees that the bug can be used to recover encrypted files.
Not long ago, a new virus (and many of its modifications) appeared on the Internet, encrypting files on your computer and offering to order a program to decrypt them for money. In this case, the encrypted files are renamed and given names like this
DSC00122.JPG. [email protected] _XO101
The selected part consists of the e-mail of the virus author (to which the “victim” of the virus will send a decryption request) and the virus modification identifier. Each modification of the virus has its own encryption algorithm and, accordingly, requires its own decryptor.
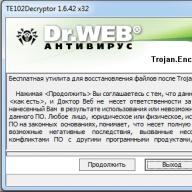
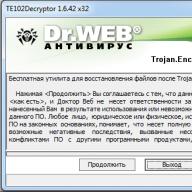
Fortunately, the developers from Dr.Web have taken up this issue closely and are ready to provide a special utility that decrypts files corrupted by the virus. For convenience, below I post the utility itself and brief instructions for using it.
(password is the name of my site without “http://”)
Below are brief instructions.
Download the recovery utility, unpack the archive into an empty folder with a simple name (for example, “ C:\_dec"). Then open the command line (Start - Run - cmd) and type the following there:
Here " [email protected] _XO101" is the prefix with which your files are renamed by the virus, pay attention to the dot at the beginning. A c:\myfiles\- this is the folder in which your encoded files are located. After launching the program will open a confirmation window

And after clicking on the “Continue” button, automatic treatment will begin. Upon completion of the program, you will receive a report, and all decoded files will be located next to the encoded ones in the folder you specified (the program does not delete encoded versions of files).

The authors of the program do not guarantee 100% treatment of all files, and I do not have the opportunity to test its operation on a large number of files, so please: whoever managed to cure files with this utility (or did not succeed) - write in the comments.
That's all! Be healthy!
P.S. To prevent the situation of your computer becoming infected from happening again, purchase it already normal antivirus. I use Kaspersky Internet Security, but apparently Dr.Web is also quite good. Believe me, one and a half thousand rubles a year for peace of mind and confidence in the future is a ridiculous price.
About a week or two ago, another hack from modern virus makers appeared on the Internet, which encrypts all the user’s files. Once again I will consider the question of how to cure a computer after a ransomware virus encrypted000007 and recover encrypted files. In this case, nothing new or unique has appeared, just a modification of the previous version.
Guaranteed decryption of files after a ransomware virus - dr-shifro.ru. Details of the work and the scheme of interaction with the customer are below in my article or on the website in the “Work Procedure” section.
Description of the CRYPTED000007 ransomware virus
The CRYPTED000007 encryptor is no fundamentally different from its predecessors. It works almost exactly the same way. But still there are several nuances that distinguish it. I'll tell you about everything in order.
It arrives, like its analogues, by mail. Social engineering techniques are used to ensure that the user becomes interested in the letter and opens it. In my case, the letter talked about some kind of court and important information about the case in the attachment. After launching the attachment, the user opens a Word document with an extract from the Moscow Arbitration Court.
In parallel with opening the document, file encryption starts. An information message from the Windows User Account Control system begins to constantly pop up.
If you agree to the proposal, then the backup copies of files in shadow copies of Windows will be deleted and restoring information will be very difficult. It is obvious that you cannot agree with the proposal under any circumstances. In this encryptor, these requests pop up constantly, one after another and do not stop, forcing the user to agree and delete the backup copies. This is the main difference from previous modifications of encryptors. I have never encountered requests to delete shadow copies without stopping. Usually, after 5-10 offers they stopped.
I will immediately give a recommendation for the future. It is very common for people to disable User Account Control warnings. There is no need to do this. This mechanism can really help in resisting viruses. The second obvious piece of advice is to not constantly work under the computer administrator account unless there is an objective need for it. In this case, the virus will not have the opportunity to do much harm. You will have a better chance of resisting him.
But even if you have always answered negatively to the ransomware’s requests, all your data is already encrypted. After the encryption process is completed, you will see a picture on your desktop.
At the same time, there will be many text files with the same content on your desktop.
Your files have been encrypted. To decrypt ux, you need to send the code: 329D54752553ED978F94|0 to the email address [email protected]. Next you will receive all the necessary instructions. Attempts to decipher on your own will not lead to anything other than an irrevocable number of information. If you still want to try, then make backup copies of the files first, otherwise, in the event of a change, decryption will become impossible under any circumstances. If you have not received notification at the above address within 48 hours (only in this case!), use the contact form. This can be done in two ways: 1) Download and install Tor Browser using the link: https://www.torproject.org/download/download-easy.html.en In the Tor Browser address, enter the address: http://cryptsen7fo43rr6 .onion/ and press Enter. The page with the contact form will load. 2) In any browser, go to one of the addresses: http://cryptsen7fo43rr6.onion.to/ http://cryptsen7fo43rr6.onion.cab/ All the important files on your computer were encrypted. To decrypt the files you should send the following code: 329D54752553ED978F94|0 to e-mail address [email protected]. Then you will receive all necessary instructions. All the attempts of decryption by yourself will result only in irrevocable loss of your data. If you still want to try to decrypt them by yourself please make a backup at first because the decryption will become impossible in case of any changes inside the files. If you did not receive the answer from the aforecited email for more than 48 hours (and only in this case!), use the feedback form. You can do it by two ways: 1) Download Tor Browser from here: https://www.torproject.org/download/download-easy.html.en Install it and type the following address into the address bar: http:/ /cryptsen7fo43rr6.onion/ Press Enter and then the page with feedback form will be loaded. 2) Go to the one of the following addresses in any browser: http://cryptsen7fo43rr6.onion.to/ http://cryptsen7fo43rr6.onion.cab/
Mailing address may change. I also came across the following addresses:
Addresses are constantly updated, so they can be completely different.
As soon as you discover that your files are encrypted, immediately turn off your computer. This must be done to interrupt the encryption process both on the local computer and on network drives. An encryption virus can encrypt all information it can reach, including on network drives. But if there is a large amount of information there, then it will take him considerable time. Sometimes, even in a couple of hours, the ransomware did not have time to encrypt everything on a network drive with a capacity of approximately 100 gigabytes.
Next you need to think carefully about how to act. If you need information on your computer at any cost and you do not have backup copies, then it is better at this moment to turn to specialists. Not necessarily for money to some companies. You just need a person who is well versed in information systems. It is necessary to assess the scale of the disaster, remove the virus, and collect all available information on the situation in order to understand how to proceed.
Incorrect actions at this stage can significantly complicate the process of decrypting or restoring files. In the worst case, they can make it impossible. So take your time, be careful and consistent.
How the CRYPTED000007 ransomware virus encrypts files
After the virus has been launched and has finished its activity, all useful files will be encrypted, renamed from extension.crypted000007. Moreover, not only the file extension will be replaced, but also the file name, so you won’t know exactly what kind of files you had if you don’t remember. It will look something like this.
In such a situation, it will be difficult to assess the scale of the tragedy, since you will not be able to fully remember what you had in different folders. This was done specifically to confuse people and encourage them to pay for file decryption.
And if your network folders were encrypted and there are no full backups, then this can completely stop the work of the entire organization. It will take you a while to figure out what was ultimately lost in order to begin restoration.
How to treat your computer and remove CRYPTED000007 ransomware
The CRYPTED000007 virus is already on your computer. The first and most important question is how to disinfect a computer and how to remove a virus from it in order to prevent further encryption if it has not yet been completed. I would like to immediately draw your attention to the fact that after you yourself begin to perform some actions with your computer, the chances of decrypting the data decrease. If you need to recover files at any cost, do not touch your computer, but immediately contact professionals. Below I will talk about them and provide a link to the site and describe how they work.
In the meantime, we will continue to independently treat the computer and remove the virus. Traditionally, ransomware is easily removed from a computer, since the virus does not have the task of remaining on the computer at any cost. After completely encrypting the files, it is even more profitable for him to delete himself and disappear, so that it is more difficult to investigate the incident and decrypt the files.
It is difficult to describe how to manually remove a virus, although I have tried to do this before, but I see that most often it is pointless. File names and virus placement paths are constantly changing. What I saw is no longer relevant in a week or two. Usually, viruses are sent by mail in waves, and each time there is a new modification that is not yet detected by antiviruses. Universal tools that check startup and detect suspicious activity in system folders help.
To remove the CRYPTED000007 virus, you can use the following programs:
- Kaspersky Virus Removal Tool - a utility from Kaspersky http://www.kaspersky.ru/antivirus-removal-tool.
- Dr.Web CureIt! - a similar product from other web http://free.drweb.ru/cureit.
- If the first two utilities do not help, try MALWAREBYTES 3.0 - https://ru.malwarebytes.com.
Most likely, one of these products will clear your computer of the CRYPTED000007 ransomware. If it suddenly happens that they do not help, try removing the virus manually. I gave an example of the removal method and you can see it there. Briefly, step by step, you need to act like this:
- We look at the list of processes, after adding several additional columns to the task manager.
- We find the virus process, open the folder in which it sits and delete it.
- We clear the mention of the virus process by file name in the registry.
- We reboot and make sure that the CRYPTED000007 virus is not in the list of running processes.
Where to download the decryptor CRYPTED000007
The question of a simple and reliable decryptor comes up first when it comes to a ransomware virus. The first thing I recommend is to use the service https://www.nomoreransom.org. What if you are lucky and they have a decryptor for your version of the CRYPTED000007 encryptor. I’ll say right away that you don’t have many chances, but trying is not torture. On the main page click Yes:

Then download a couple of encrypted files and click Go! Find out:

At the time of writing, there was no decryptor on the site.

Perhaps you will have better luck. You can also see the list of decryptors for download on a separate page - https://www.nomoreransom.org/decryption-tools.html. Maybe there's something useful there. When the virus is completely fresh, there is little chance of this happening, but over time, something may appear. There are examples when decryptors for some modifications of encryptors appeared on the network. And these examples are on the specified page.
I don’t know where else you can find a decoder. It is unlikely that it will actually exist, taking into account the peculiarities of the work of modern encryptors. Only the authors of the virus can have a full-fledged decryptor.
How to decrypt and recover files after the CRYPTED000007 virus
What to do when the CRYPTED000007 virus has encrypted your files? The technical implementation of encryption does not allow decrypting files without a key or a decryptor, which only the author of the encryptor has. Maybe there is some other way to get it, but I don't have that information. We can only try to recover files using improvised methods. These include:
- Tool shadow copies windows.
- Deleted data recovery programs
First, let's check if we have shadow copies enabled. This tool works by default in Windows 7 and higher, unless you manually disable it. To check, open the computer properties and go to the system protection section.

If during infection you did not confirm the UAC request to delete files in shadow copies, then some data should remain there. I spoke in more detail about this request at the beginning of the story, when I talked about the work of the virus.
To easily restore files from shadow copies, I suggest using a free program for this - ShadowExplorer. Download the archive, unpack the program and run it.
The latest copy of files and the root of drive C will open. In the upper left corner, you can select a backup copy if you have several of them. Check different copies for the required files. Compare by date for the most recent version. In my example below, I found 2 files on my desktop from three months ago when they were last edited.

I was able to recover these files. To do this, I selected them, right-clicked, selected Export and specified the folder where to restore them.

You can restore folders immediately using the same principle. If you had shadow copies working and did not delete them, you have a good chance of recovering all, or almost all, files encrypted by the virus. Perhaps some of them will be an older version than we would like, but nevertheless, it is better than nothing.
If for some reason you do not have shadow copies of your files, your only chance to get at least something from the encrypted files is to restore them using deleted file recovery tools. To do this, I suggest using the free program Photorec.
Launch the program and select the disk on which you will restore files. Launching the graphical version of the program executes the file qphotorec_win.exe. You must select a folder where the found files will be placed. It is better if this folder is not located on the same drive where we are searching. Connect a flash drive or external hard drive to do this.

The search process will take a long time. At the end you will see statistics. Now you can go to the previously specified folder and see what is found there. There will most likely be a lot of files and most of them will either be damaged or they will be some kind of system and useless files. But nevertheless, some useful files can be found in this list. There are no guarantees here, what you find is what you will find. Images are usually restored best.
If the result does not satisfy you, then there are also programs for recovering deleted files. Below is a list of programs that I usually use when I need to recover the maximum number of files:
- R.saver
- Starus File Recovery
- JPEG Recovery Pro
- Active File Recovery Professional
These programs are not free, so I will not provide links. If you really want, you can find them yourself on the Internet.
The entire file recovery process is shown in detail in the video at the very end of the article.
Kaspersky, eset nod32 and others in the fight against the Filecoder.ED encryptor
Popular antiviruses detect the ransomware CRYPTED000007 as Filecoder.ED and then there may be some other designation. I looked through the major antivirus forums and didn't see anything useful there. Unfortunately, as usual, antivirus software turned out to be unprepared for the invasion of a new wave of ransomware. Here is a post from the Kaspersky forum.
Antiviruses traditionally miss new modifications of ransomware Trojans. Nevertheless, I recommend using them. If you are lucky and receive a ransomware email not in the first wave of infections, but a little later, there is a chance that the antivirus will help you. They all work one step behind the attackers. A new version of ransomware is released, but antiviruses do not respond to it. As soon as a certain amount of material for research on a new virus accumulates, antivirus software releases an update and begins to respond to it.
I don’t understand what prevents antiviruses from responding immediately to any encryption process in the system. Perhaps there is some technical nuance on this topic that does not allow us to adequately respond and prevent encryption of user files. It seems to me that it would be possible to at least display a warning about the fact that someone is encrypting your files, and offer to stop the process.
Where to go for guaranteed decryption
I happened to meet one company that actually decrypts data after the work of various encryption viruses, including CRYPTED000007. Their address is http://www.dr-shifro.ru. Payment only after full decryption and your verification. Here is an approximate scheme of work:
- A company specialist comes to your office or home and signs an agreement with you, which sets out the cost of the work.
- Launches the decryptor and decrypts all files.
- You make sure that all files are opened and sign the certificate of delivery/acceptance of completed work.
- Payment is made solely upon successful decryption results.
I'll be honest, I don't know how they do it, but you don't risk anything. Payment only after demonstration of the decoder's operation. Please write a review about your experience with this company.
Methods of protection against the CRYPTED000007 virus
How to protect yourself from ransomware and avoid material and moral damage? There are some simple and effective tips:
- Backup! Backup of all important data. And not just a backup, but a backup to which there is no constant access. Otherwise, the virus can infect both your documents and backup copies.
- Licensed antivirus. Although they do not provide a 100% guarantee, they increase the chances of avoiding encryption. They are most often not ready for new versions of the encryptor, but after 3-4 days they begin to respond. This increases your chances of avoiding infection if you were not included in the first wave of distribution of a new modification of the ransomware.
- Do not open suspicious attachments in mail. There is nothing to comment here. All ransomware known to me reached users via email. Moreover, every time new tricks are invented to deceive the victim.
- Do not thoughtlessly open links sent to you from your friends via social networks or instant messengers. This is also how viruses sometimes spread.
- Enable windows to display file extensions. How to do this is easy to find on the Internet. This will allow you to notice the file extension on the virus. Most often it will be .exe, .vbs, .src. In your everyday work with documents, you are unlikely to come across such file extensions.
I tried to supplement what I have already written before in every article about the ransomware virus. In the meantime, I say goodbye. I would be glad to receive useful comments on the article and the CRYPTED000007 ransomware virus in general.
Video about file decryption and recovery
Here is an example of a previous modification of the virus, but the video is completely relevant for CRYPTED000007.
Recently, the 360 Internet Security Center discovered a new type of ransomware virus targeting both businesses and individuals in many countries and regions. 360 issued a timely emergency warning on May 12 following the discovery to remind users of the upcoming risks. This ransomware is spreading at high speed throughout the world. According to incomplete statistics, tens of thousands of devices in 99 countries were infected in just a few hours after the explosion, and this network worm is still trying to expand its influence.
Typically, a ransomware virus is a malicious program with the clear intent of extortion. It encrypts the victim's files using an asymmetric cryptographic algorithm, makes them inaccessible, and demands a ransom to decrypt them. If the ransom is not paid, the files cannot be recovered. This new species is codenamed WanaCrypt0r. What makes him so deadly is that he used the hacking tool "EternalBLue" which was stolen from the NSA. This also explains why WanaCrypt0r was able to spread quickly throughout the world and caused large losses in a very short time. After the network worm breakthrough on May 12, the Core Security department at the 360 Internet Security Center conducted thorough monitoring and in-depth analysis. We can now release a suite of detection, protection and data recovery solutions against WanaCrypt0r.
360 Helios Team is an APT (Advanced Persistent Attack) research and analysis team within the Core Security department, primarily dedicated to APT attack investigation and threat incident response. Security researchers have carefully analyzed the mechanism of viruses to find the most effective and accurate method for recovering encrypted files. Using this method, 360 can become the first security provider to release a data recovery tool - "360 Ransomware Infected File Recovery" to help its customers recover infected files quickly and completely. We hope this article helps you understand the tricks of this worm, as well as the broader discussion about recovering encrypted files.
Chapter 2 Analysis of Basic Encryption Processes
This worm exposes the encryption module into memory and directly loads the DLL into memory. The DLL then exports a TaskStart function that should be used to activate the entire encryption process. The DLL dynamically accesses the file system and encryption-related API functions to avoid static detection.
1.Initial stage
It first uses "SHGetFolderPathW" to get the desktop and file folder paths. It will then call the "10004A40" function to get the path to other users' desktops and file folders and call the EncrytFolder function to encrypt the folders individually.



It scans all drives twice from driver Z to C. The first scan is to run all local drives (except driver-CD). The second scan checks all mobile storage devices and calls the EncrytFolder function to encrypt files.

2.File traverse
The "EncryptFolder" function is a recursive function that can collect information about files by following the procedure below:

Remove file paths or folders during the cross process:

There is an interesting folder called “This folder protects against ransomware. Changing it will reduce the protection." When you do this, you will find that it corresponds to the protection folder of the anti-ransomware software.
While crawling files, ransomware collects information about the file, such as the size of the files, and then classifies the files into different types according to their extension, following certain rules:

List of extension types 1:

List of extension types 2:

3.Encryption priority
To encrypt important files as quickly as possible, WanaCrypt0r has developed a complex priority queue:
Priority queue:
I.Encrypt files of type 2 that also match extension list 1. If the file is smaller than 0X400, the encryption priority will be lowered.
II. Encrypt files of type 3 that also match extension list 2. If the file is smaller than 0X400, the encryption priority will be lowered.
III. Encrypt the remaining files (less than 0x400) and other files.
4.Encryption logic
The entire encryption process is completed using both RSA and AES. Although the RSA encryption process uses the Microsoft CryptAPI, the AES code is statically compiled into a DLL. The encryption process is shown in the figure below:

List of used keys:

File format after encryption:

Please note that during the encryption process, the ransomware will randomly select some files to encrypt, using the built-in RSA public key to offer a few files that victims can decrypt for free.

The path to the free files can be found in the file "f.wnry".

5.Filling in random numbers
Once encrypted, WanaCrypt0r will fill files it deems important with random numbers until it completely destroys the file, then move the files to a temporary file directory for deletion. By doing this, it makes it quite difficult for file recovery tools to recover files. At the same time, it can speed up the encryption process.
Completed files must meet the following requirements:
— In the specified directory (desktop, my document, user folder)
— The file is less than 200 MB
— The file extension is in the list of extension types 1
File filling logic:
- If the file is less than 0x400, it will be covered with random numbers of the same length
- If the file is larger than 0x400, the last 0x400 will be covered with random numbers
- Move the file pointer to the file header and set 0x40000 as the data block to cover the file with random numbers until the end.

6.Deleting files
WanaCrypt0r will first move files to a temporary folder to create a temporary file, and then delete it in various ways.
When it goes through the drives to encrypt files, it will create a temporary file named in the format "$RECYCLE + auto increment + .WNCYRT" (for example: "D:\$RECYCLE\1.WNCRYT") on the current drive. Especially if the current drive is a system drive (such as Driver-C), it will use the system's temporary directory.

Subsequently, the process runs taskdl.exe and deletes temporary files at a fixed time interval.
Chapter 3 Data Recovery Possibility
In analyzing its execution logic, we noticed that this worm will overwrite files that meet the specified requirements with random numbers or 0x55 to destroy file structures and prevent their recovery. But this operation is accepted only for certain files or files with a certain extension. This means that there are still many files that have not been overwritten, leaving room for file recovery.
During the removal process, the worm moved the source files to a temporary files folder by calling the MoveFileEx function. Eventually the temporary files are deleted en masse. During the above process, the original files may be modified, but the current data recovery software on the market is not aware of this, so quite a few files cannot be recovered successfully. The need for recovery files for victims is almost impossible to realize.
For other files, the worm simply executed the "move & delete" command. Since the processes of deleting files and moving files are separate, the two threads will compete with each other, which may cause the file movement to fail due to differences in the user's system environment. This will delete the file directly in its current location. In this case, there is a high probability that the file can be recovered.
https://360totalsecurity.com/s/ransomrecovery/
Using our recovery methods, a large percentage of encrypted files can be recovered perfectly. Now, the updated 360 version of the file recovery tool has been developed in response to this need to help tens of thousands of victims mitigate losses and consequences.
May 14, 360 is the first security vendor to release a file recovery tool that has saved many files from ransomware. This new version takes another step in exploiting WanaCrypt0r's logical vulnerabilities. It can remove the virus to prevent further infection. Using multiple algorithms, it can find hidden connections between free recoverable files and decrypted files for clients. This all-in-one recovery service can reduce the damage from a ransomware attack and protect the security of users' data.
Chapter 4 Conclusion
Mass outbreak and spread of WannaCry worms through the use of MS17-010, which makes it capable of self-replication and active propagation, in addition to the functions of a general ransomware. Apart from the attack payload, the technical structure of the ransomware plays the most important role in the attacks. The ransomware encrypts the AES key using the asymmetric cryptographic algorithm RSA-2048. Each file is then encrypted using a random AES-128 symmetric encryption algorithm. This means, relying on existing calculations and methods, it is almost impossible to decrypt RSA-2048 and AES-128 without any public or private keys. However, the authors leave some errors in the encryption process, which ensures and increases the possibility of recovery. If the actions are performed quickly enough, most of the data can be saved back.
Additionally, since the ransom money is paid in anonymous Bitcoins, for which anyone can obtain the address without true certification, it is impossible to identify the attacker across addresses, let alone between different accounts of the same address owner. Therefore, due to the adoption of an unbreakable encryption algorithm and anonymous Bitcoins, it is highly likely that this type of profitable ransomware outbreak will continue for a long time. Everyone must be careful.
360 Helios Team
360 Helios Team is an APT (Advanced Persistent Attack) research team in Qihoo 360.
The team is dedicated to investigating APT attacks, responding to threat incidents, and researching the industrial chains of the underground economy.
Since its inception in December 2014, the team has successfully integrated a huge 360 database and created a fast reversal and correlation process. To date, more than 30 APTs and underground economy groups have been identified and identified.
360 Helios also provides threat assessment and response solutions for enterprises.
Public reports

Contact
Email Mail: [email protected]
WeChat Group: 360 Helios Team
Please download the QR code below to follow us on WeChat!

If a text message appears on your computer saying that your files are encrypted, then do not rush to panic. What are the symptoms of file encryption? The usual extension changes to *.vault, *.xtbl, * [email protected] _XO101, etc. The files cannot be opened - a key is required, which can be purchased by sending a letter to the address specified in the message.
Where did you get the encrypted files from?
The computer caught a virus that blocked access to information. Antivirus programs often miss them because the program is usually based on some harmless free encryption utility. You will remove the virus itself quickly enough, but serious problems may arise with decrypting the information.
Technical support from Kaspersky Lab, Dr.Web and other well-known companies developing anti-virus software, in response to user requests to decrypt data, reports that it is impossible to do this in an acceptable time. There are several programs that can pick up the code, but they can only work with previously studied viruses. If you encounter a new modification, then the chances of restoring access to information are extremely low.
How does a ransomware virus get onto a computer?
In 90% of cases, users themselves activate the virus on their computer, opening unknown letters. Then a message is sent to e-mail with a provocative subject - “Subpoena”, “Loan debt”, “Notification from the tax office”, etc. Inside the fake letter there is an attachment, after downloading which the ransomware gets onto the computer and begins to gradually block access to the files.
Encryption does not happen instantly, so users have time to remove the virus before all information is encrypted. You can destroy a malicious script using the cleaning utilities Dr.Web CureIt, Kaspersky Internet Security and Malwarebytes Antimalware.
File recovery methods
If system protection has been enabled on your computer, then even after the effect of a ransomware virus there is a chance to return files to their normal state using shadow copies of files. Ransomware usually tries to remove them, but sometimes they fail to do so due to lack of administrator rights.
Restoring a previous version:

In order for previous versions to be saved, you need to enable system protection.
Important: system protection must be enabled before the ransomware appears, after which it will no longer help.
- Open Computer properties.

- From the menu on the left, select System Protection.

- Select drive C and click "Configure".

- Choose to restore settings and previous versions of files. Apply the changes by clicking "Ok".

If you took these steps before the file-encrypting virus appeared, then after cleaning your computer from malicious code, you will have a good chance of recovering your information.
Using special utilities
Kaspersky Lab has prepared several utilities to help open encrypted files after removing the virus. The first decryptor you should try is Kaspersky RectorDecryptor.
- Download the program from the official Kaspersky Lab website.
- Then run the utility and click “Start scan”. Specify the path to any encrypted file.
If the malicious program has not changed the extension of the files, then to decrypt them you need to collect them in a separate folder. If the utility is RectorDecryptor, download two more programs from the official Kaspersky website - XoristDecryptor and RakhniDecryptor. 
The latest utility from Kaspersky Lab is called Ransomware Decryptor. It helps decrypt files after the CoinVault virus, which is not yet very widespread on the RuNet, but may soon replace other Trojans.